Langkah 2: Capture Data dan Hack Wifi Dengan Wireshark. Pertama silahkan anda setting wireshark rubah wirelles interface ke 802.11 client device. Dan klik Menu Capture, pilih optin dan pilih interface. Rubah RF Channe 1, setting wireshark ke channel dengan cara pilih Option, lalu pilih Interface. May 24, 2015 - Detailed Step-by-Step tutorial on how to do a Pixie Dust Attack WPS in Kali. When a wireless router is vulnerable for this attack retrieving the.
Eduard kraft torrent. 2,138 Followers, 36 Following, 43 Posts - See Instagram photos and videos from Eduard Kraft (@ikraft).
Share • LinkedIn • Facebook • Twitter 2 Wireshark is the world’s foremost network protocol analyzer.  It lets you see what’s happening on your network at a microscopic level. It is the de facto (and often de jure) standard across many industries and educational institutions. This tutorial can be an angel and also devil in the same time, it depends to you who use this tutorial for which purposeme as a writer of this tutorial just hope that all of you can use it in the right way, because I believe that no one from you want your password sniffed by someone out there so don’t do that to others too Disclaimer – Our tutorials are designed to aid aspiring pen testers/security enthusiasts in learning new skills, we only recommend that you test this tutorial on a system that belongs to YOU.
It lets you see what’s happening on your network at a microscopic level. It is the de facto (and often de jure) standard across many industries and educational institutions. This tutorial can be an angel and also devil in the same time, it depends to you who use this tutorial for which purposeme as a writer of this tutorial just hope that all of you can use it in the right way, because I believe that no one from you want your password sniffed by someone out there so don’t do that to others too Disclaimer – Our tutorials are designed to aid aspiring pen testers/security enthusiasts in learning new skills, we only recommend that you test this tutorial on a system that belongs to YOU.
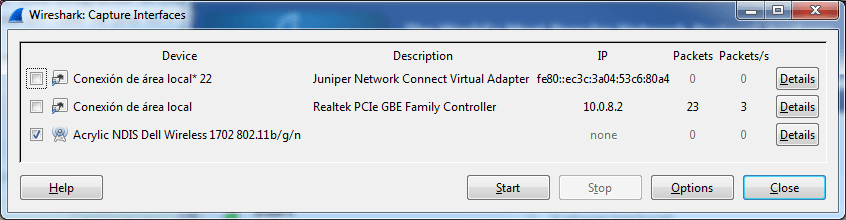
We do not accept responsibility for anyone who thinks it’s a good idea to try to use this to attempt to hack systems that do not belong to you Requirements: 1. Wireshark Network Analyzer (wireshark.org) 2. Network Card (Wi-Fi Card, LAN Card, etc) fyi: for wi-fi it should support promiscious mode Step 1: Start Wireshark and capture traffic In Kali Linux you can start Wireshark by going to Application > Kali Linux > Top 10 Security Tools > Wireshark In Wireshark go to Capture > Interface and tick the interface that applies to you. In my case, I am using a Wireless USB card, so I’ve selected wlan0.
Step 2: Filter captured traffic for POST data At this point Wireshark is listening to all network traffic and capturing them. I opened a browser and signed in a website using my username and password. When the authentication process was complete and I was logged in, I went back and stopped the capture in Wireshark. When wee type in your username, password and press the Login button, it generates a a POST method (in short – you’re sending data to the remote server). To filter all traffic and locate POST data, type in the following in the filter section http.request.method == “POST” See screenshot below.
It is showing 1 POST event.